Security Trust Center
Scholarship America aims to eliminate financial barriers to students’ dreams. For more than 60 years, we’ve worked with sponsors of all sizes to craft flexible scholarship programs that connect organizations’ missions with best-in-class solutions.
Scholarship America is deeply committed to safeguarding the security, safety, and privacy of our sponsors and students’ data. Our controls follow the National Institute of Standards and Technology (NIST) framework to ensure security, confidentiality, and robust service delivery.
The Scholarship America Trust Center provides insight into our security controls and our sub processors.
Controls
Organizational Security
Background Checks
Confidentiality Agreements Acknowledge
Information Security Program / Security Policy Manual
1 more Organizational Security security controls
Product Security
Annual Pen Testing
Application Monitoring Solution
Customer Identity and Access Management
5 more Product Security security controls
Internal Security Procedures
Access Request Policies and Procedures Established
Annual Developer Security Training
Annual Report to the Board or Senior Management
16 more Internal Security Procedures security controls
Infrastructure Security
Backup System
Centralized Logging
Cloud Based and On-Premise Firewalls
18 more Infrastructure Security security controls
Subprocessors

Amazon Web Services • Infrastructure Hosting
Click the link to review the Amazon Web Services Trust Center.

Microsoft • Infrastructure Hosting
Click the link to review the Microsoft Trust Center.

Submittable • Scholarship Management System
Click the link to review the Submittable Trust Center.

SideChannel • vCISO
3 more Subprocessors
Controls
Organizational Security
| Control | Status |
|---|---|
|
Background Checks Scholarship America performs background checks on employees. |
|
|
Confidentiality Agreements Acknowledge Scholarship America requires and includes confidentiality agreements in contracts and maintains confidential policies and agreements for its staff. |
|
|
Information Security Program / Security Policy Manual Scholarship America manages its security practices with up-to-date policies and strict compliance programs. |
|
|
vCISO Scholarship America engages an experienced and certified vCISO, SideChannel, for additional support navigating its Security concern. |
Product Security
| Control | Status |
|---|---|
|
Annual Pen Testing Scholarship America performs annual pen testing on applications and the external network where the vulnerabilities found are triaged, planned, and remediated to the plan. |
|
|
Application Monitoring Solution Scholarship America monitors application and infrastructure on a continuous basis that can be cross-correlated and detects DOS/DDOS for unexpected traffic spikes. |
|
|
Customer Identity and Access Management Scholarship America uses a CIAM system on its core student platform. |
|
|
Infrastructure Monitoring Solution Scholarship America monitors system and networks for performance and high traffic utilization. |
|
|
Static Code Analysis Tool (SAST) Scholarship America scans its Static Code Analysis tool on release for vulnerabilities. |
|
|
Vulnerability System and Web Application Scanning Tool Scholarship America scans vulnerability weekly for both systems and applications. |
|
|
Web Application Firewall Scholarship America protects its external-facing web applications with best-in-class firewalls. |
|
|
Workstation Monitoring (RMM) Solution and Cloud Based Patching Scholarship America engages workstation monitor and cloud-based patching to remediate vulnerabilities when detected. |
Internal Security Procedures
| Control | Status |
|---|---|
|
Access Request Policies and Procedures Established Scholarship America follows least privileged access when granting access to in-scope systems and requires that a formal request and approval process is followed. |
|
|
Annual Developer Security Training Scholarship America conducts annual developer security awareness training following OWASP and best practices. |
|
|
Annual Report to the Board or Senior Management Scholarship America provides an annual report to members of its board and senior management. |
|
|
Annual Risk Assessment Scholarship America engages a third party to perform an annual risk assessment where findings are triaged and remediated based on its findings. |
|
|
Annual Security Awareness Training Scholarship America conducts annual security awareness training following OWASP and best practices for all employees and contractors. |
|
|
Biannual User Reviews Scholarship America conducts biannual reviews of system access to make sure all users still require the access that fit their role. |
|
|
Board Meetings Conducted Scholarship America’s Board of Trustees meets at least 3 times a year, maintains formal meeting minutes, and is comprised of independent, highly qualified members. |
|
|
Configuration Management Policy and Procedure Scholarship America’s configuration management policy and procedure documents and requires approval for changes to the systems and network. |
|
|
Disaster Recovery Plan Scholarship America follows a detailed organizational disaster recovery plan with defined RTO and RPO. |
|
|
Disaster Recovery Testing Scholarship America conducts a bi-annual test of the disaster recovery plan. |
|
|
Incident Response Plan Scholarship America follows a detailed an organizational incident response plan with defined RTO and RPO. |
|
|
Incident Response Testing Scholarship America conducts a bi-annual test of the incident response plan. |
|
|
Monthly Phishing Tests Scholarship America conducts regular phishing tests for its staff and contractors. |
|
|
Organization Structure Documented Scholarship America’s organizational chart describes the organization structure and reporting structure. |
|
|
Specialized Security Training for Security Personnel Scholarship America requires personnel in a security role to do advanced security training annually. |
|
|
Third Party Risk Assessments Scholarship America performs third party risk assessments on all vendors and third-party contractors. |
|
|
Ticketing System for Incidents and Access Requests Scholarship America maintains a ticket system for managing incidents, problems, and access requests. |
|
|
Vulnerability Notification from Reputable Sources (i.e. CISA newsletter) Scholarship America actively monitors newsletters and other media for critical vulnerabilities published by reputable sources. |
|
|
Whistle Blower Policy Scholarship America engages a formalized whistle blower policy with an anonymous communication channel in place for users report potential issues or fraud concerns. |
Infrastructure Security
| Control | Status |
|---|---|
|
Backup System Scholarship America conducts industry standard backups on a regular cadence. |
|
|
Centralized Logging Scholarship America maintains a centralized logging system for security and performance monitoring. |
|
|
Cloud Based and On-Premise Firewalls Scholarship America protects all its data environments with best-in-class firewalls. |
|
|
DMARC, SPF, and DKIM Rules In Place Scholarship America follows SPAM-CAN rules to prevent fraudulent email from being sent through its mail servers and to reduce phishing attempts. |
|
|
Email Filtering with Advanced Threat Protection Scholarship America monitors email for common and advanced threats. |
|
|
Endpoint Detection and Response Scholarship America maintains end point detection and response systems for detecting and cleaning malware/viruses that is used to prevent unapproved devices from connecting to the system and monitoring for unusual behavior. |
|
|
IDS / IPS Scholarship America uses intrusion detection and intrusion prevention measures. |
|
|
Industry Standard Encryption at Rest Scholarship America follows or exceeds industry standard encryption at rest. |
|
|
Industry Standard Encryption in Transit Scholarship America follows or exceeds industry standard encryption in transit. |
|
|
Inventory Management Solution Scholarship America maintains an inventory of its hard and software assets. |
|
|
Managed Extended Detection and Response / Security Operation Center The company has 24 hour x 7 days a week x 365 days a year log monitoring to detect intruders and malicious activity. |
|
|
Mobile Device Management (MDM) on Laptops Scholarship America manages its laptops and other devices with MDM that allows lost or stolen devices to be wiped. |
|
|
Network Segmentation Scholarship America segments its network to prevent unauthorized access to protected and secure data. |
|
|
Privilege Access Management System Scholarship America uses a PAM to control, administer, and monitor privilege access to systems. |
|
|
Public Credential Dump Monitoring Scholarship America continuously monitors for data that has been disclosed or scraped. |
|
|
Remote Access Encryption Enforced Scholarship America’s systems can only be remotely accessed by authorized staff via an approved encrypted connection. |
|
|
SSO / MFA solution Scholarship America uses a single sign-on/multi-factor authentication solution to manage access to internal and third-party systems. |
|
|
System Hardening Scholarship America follows the Center for Information Security Benchmarks for hardening systems. |
|
|
System Imaging Scholarship America maintains system images with embedded security controls when deploying out systems. |
|
|
System Wiping to NIST standards Scholarship America follows NIST framework when wiping systems during the decommissioning process and shreds drives if the drive is unable to be wiped. |
|
|
WIFI Security Scholarship America secures its WIFI system with the industry standard. |
Subprocessors

Amazon Web Services • Infrastructure Hosting
Click the link to review the Amazon Web Services Trust Center.

Microsoft • Infrastructure Hosting
Click the link to review the Microsoft Trust Center.

Submittable • Scholarship Management System
Click the link to review the Submittable Trust Center.

SideChannel • vCISO

Blackbaud • CRM Platform
Click the link to review the Blackbaud Trust Center.

J.P. Morgan • Check Processing
Click the link to review the J.P. Morgan Trust Center.

TestingXperts • System Development, Quality Assurance and Quality Control
Scholarship America Overall Results
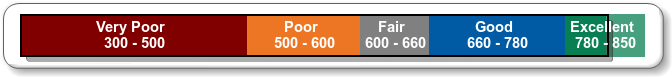
The overall S2SCORE (or risk rating) is 816.08.
816.08
Excellent
A S2SCORE of 816.08 translate to “Excellent”. In general, a S2SCORE in this range means that all critical controls and safeguards have been implemented to protect organizational assets including additional compensating controls. There are no identified vulnerabilities in the presence of applicable threats at his time. Potential impact would be localized to the project level with minimal financial loss.
The S2SCORE is calculated in a range from 300 to 850. The lower the score, the higher the risk. And vice versa. A S2SCORE of 660.00 or “Good” is acceptable to most organizations and should be the goal for Scholarship America.
S2SCORE Scale